Beyond the Firewall: Why LPWA IoT Demands a Three-Layer Security Architecture
Enterprise firewalls and network-layer security were never designed for the unique protocols and constraints of LPWA IoT. Learn how a layered approach — from cellular network to enterprise firewall to application-level deep packet inspection — closes the gap.

Beyond the Firewall: Why LPWA IoT Demands a Three-Layer Security Architecture
The Internet of Things is under siege. Deloitte's 2024 Cyber Threat Trends Report documented a 400% increase in IoT malware attacks, and Forrester predicted that a major IoT breach would disrupt an entire class of devices by 2025. With over 21 billion connected devices worldwide in 2026 — and roughly 29% of them communicating over cellular or LPWAN networks — the attack surface is enormous, growing, and unlike anything traditional IT security was built to handle.
For enterprises deploying LPWA (Low Power Wide Area) IoT at scale — think asset trackers, smart meters, environmental sensors, fleet telematics, and industrial monitors — the security conversation has fundamentally changed. It's no longer about whether you need security, but about how many layers you need and where the critical gaps are hiding.
This post introduces a three-layer security architecture for LPWA IoT that addresses the full data path: from the cellular network, through the enterprise perimeter, and deep into the application data itself.
The Threat Landscape Has Changed
IoT devices are not laptops. They don't run endpoint agents. They can't be patched with a group policy push. Many LPWA devices operate on microcontrollers with kilobytes of RAM, communicate over constrained protocols like CoAP and LWM2M, and are deployed in locations where physical access is impossible or impractical.
This makes them ideal targets. One in three data breaches now involves an IoT device. Unpatched firmware accounts for an estimated 60% of IoT security breaches. And the consequences have moved beyond data theft into the realm of physical safety — compromised devices in critical infrastructure, fleet management, and healthcare can cause real-world harm.
The traditional IT security playbook: install an agent, segment the VLAN, patch quarterly simply doesn't apply to LPWA IoT. A new playbook is needed, one that layers security at every point in the data path where intelligence can be applied.

Layer 1: Network-Level Security — The Cellular Provider
The first layer of defense for cellular LPWA IoT sits within the mobile network itself. Cellular providers have unique visibility into device behavior at the network level: which destinations devices communicate with, how much data they transfer, what ports and protocols they use, and when behavior deviates from established patterns.
The State of the Art: Aeris IoT Watchtower
Aeris, a global leader in cellular IoT platforms, launched IoT Watchtower in early 2025 as what they describe as the first fully integrated security solution for cellular IoT. The platform operates inline with the cellular data path and requires no agents, no special SIM cards, and no proxy infrastructure. It applies Zero Trust security principles at the network layer.
Watchtower provides two core capabilities. The Awareness side delivers deep visibility into device behavior, traffic patterns, and threat detection using AI and known threat databases across Aeris's network of 25+ mobile operators. The Enforcement side enables policy-based access controls, automated malware blocking, and the ability to quarantine compromised devices at the SIM level.
After monitoring roughly 600,000 smart devices, Aeris reported alarming levels of device communication with dark web destinations, botnets, command-and-control servers, and known phishing sites. This kind of network-layer intelligence is invaluable, it catches threats that individual enterprises would never see on their own.
What Network-Layer Security Does Well
- Traffic-level threat detection: Identifies malicious destinations, anomalous data volumes, and suspicious communication patterns
- Zero Trust enforcement: Restricts device access to only approved destinations and services
- SIM-level control: Can suspend or quarantine individual SIMs in response to detected threats
- Frictionless deployment: No device-side changes required
- Scale: Operates across entire carrier networks, providing fleet-wide visibility
Where Network-Layer Security Stops
Network-layer security operates on IP traffic metadata like destinations, ports, protocols, and volumes. It does not decrypt device payloads. It cannot inspect the application-level content of a CoAP message, validate whether a GNSS location report is within expected geofence boundaries, or determine whether a device is running outdated firmware based on its LWM2M registration objects.
This is by design. Cellular providers are not in the business of deep packet inspection of customer data. Their role is to secure the pipe, not interpret what flows through it.
Layer 2: Enterprise Firewall Security — Palo Alto, Fortinet, and the Perimeter
The second layer of defense sits at the enterprise perimeter, where next-generation firewalls (NGFWs) from vendors like Palo Alto Networks and Fortinet provide IoT-specific security capabilities.
Palo Alto Networks: Device Security (Enterprise IoT Security)
Palo Alto's Device Security solution integrates with their next-generation firewalls to discover and classify IoT devices using machine learning. The platform collects network traffic metadata, identifies devices through a three-tier deep-learning engine (category, profile, and identity), and generates security policy recommendations that can be imported directly into firewall rules via Device-ID.
The system monitors over 2,000 device attributes and uses AI to establish behavioral baselines for each device type, alerting when devices deviate from expected patterns.
Fortinet: OT/IoT Security Fabric
Fortinet takes a similar approach through their Security Fabric, combining FortiGate NGFWs with the FortiGuard OT Security Service. Their solution provides deep packet inspection for industrial protocols, automated virtual patching for legacy OT devices, and integration with FortiNAC for network access control. Fortinet supports more than twice the OT protocol signatures of competing solutions, covering a broad range of industrial communication standards.
Both vendors also offer SIEM integration, Palo Alto through Strata Logging Service and XSOAR, Fortinet through FortiSIEM and FortiSOC, enabling centralized security operations.
| What Enterprise Firewalls See | What LPWA IoT Actually Uses |
|---|---|
|
|
Enterprise firewalls were designed for IT and OT, not for constrained LPWA protocols.
What Enterprise Firewalls Do Well
- Device discovery and classification: ML-driven identification of devices on the network
- Behavioral baselining: Detects when devices deviate from normal traffic patterns
- Policy enforcement: Applies granular access control rules based on device identity
- OT protocol awareness: Deep packet inspection for industrial protocols like Modbus, BACnet, and DNP3
- Automated response: Can isolate or quarantine devices based on threat detection
Where Enterprise Firewalls Fall Short for LPWA IoT
Here's the critical gap: enterprise firewalls are built for IT and OT environments where devices communicate over TCP/IP, HTTP/HTTPS, MQTT over TLS, and established industrial protocols. They excel at inspecting traffic that follows these patterns.
LPWA IoT devices don't follow these patterns.
A typical NB-IoT asset tracker communicates using CoAP over UDP, secured with DTLS (not TLS), sending CBOR-encoded or proprietary binary payloads of 50 to 512 bytes at intervals measured in hours or days. The device may register with an LWM2M server, exchanging structured object data that describes its firmware version, battery level, GNSS coordinates, signal quality, and sensor readings. Because of the long durations of device sessions, a session may be inactive for days at a time which is typically beyond the time that enterprise firewalls can inspect.
Enterprise firewalls can see that UDP traffic is flowing to a particular destination on a particular port. They might classify the device as "IoT" based on traffic patterns. But they cannot:
- Decode the CoAP message structure to understand the request method, options, and payload
- Validate DTLS session parameters to detect misconfigurations, expired certificates, or downgraded cipher suites
- Parse LWM2M objects to extract firmware versions, configuration parameters, or device state
- Interpret CBOR or proprietary binary payloads to validate location data, sensor readings, or operational parameters
- Compare individual device configurations against fleet-wide baselines to identify outliers
This isn't a criticism of Palo Alto or Fortinet — their products are exceptional at what they're designed to do. But LPWA IoT operates in a protocol and payload space that falls outside their inspection capabilities. The result is a blind spot: devices can communicate through the firewall, pass basic behavioral checks, and still be running compromised firmware, reporting fabricated location data, or operating with DTLS parameters that leave them exposed to man-in-the-middle attacks.
Layer 3: Application-Level Security — The Tartabit IoT Bridge
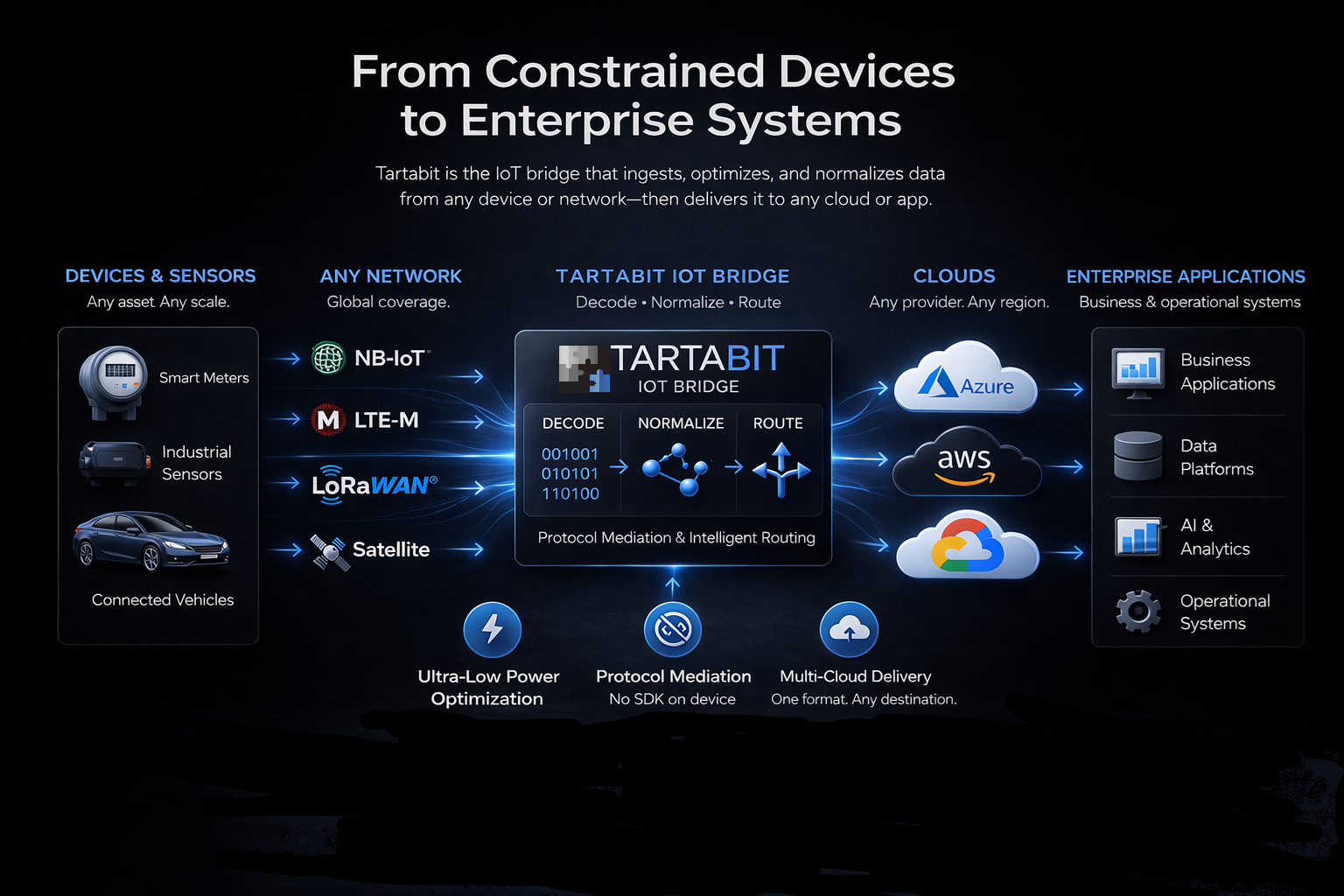
This is where the Tartabit IoT Bridge introduces a fundamentally different capability. As middleware that sits between LPWA devices and enterprise applications, the IoT Bridge is purpose-built to decode, process, and act on the actual content of LPWA IoT communications.
The IoT Bridge isn't a firewall in the traditional sense. It's an application-layer security platform — an intelligent inspection point that operates on decrypted, decoded device data with full protocol awareness for CoAP, DTLS, LWM2M, UDP, LoRaWAN, and proprietary binary formats.
Think of it as deep packet inspection (DPI) purpose-built for LPWA IoT.
What Application-Layer Security Enables
Protocol-Aware Deep Packet Inspection
The IoT Bridge decodes LPWA protocols natively. When a device sends a CoAP POST with a CBOR-encoded payload over DTLS, the IoT Bridge doesn't just see UDP bytes. It understands the CoAP message structure, validates the DTLS handshake parameters, and decodes the CBOR payload into structured data.
This enables inspection at a depth that no network-layer or perimeter security tool can achieve:
- CoAP method and option validation: Is this device sending expected message types? Are the URI paths and content formats correct?
- DTLS session inspection: Are the cipher suites appropriate? Has the device fallen back to a weaker security profile? Are pre-shared keys properly configured?
- LWM2M object parsing: What firmware version is this device running? What are its current configuration parameters? When was it last updated?
Location Data Validation
For devices reporting GNSS, WiFi-based, or cell-tower-derived location data, the IoT Bridge can apply intelligent validation: Is the reported location within expected operating boundaries? Has the device jumped an impossible distance between reports? Is the location data internally consistent (e.g., does the reported cell tower match the expected coverage area)?
Fabricated or spoofed location data is a growing concern in fleet management and asset tracking. Traditional firewalls have no mechanism to detect it because they don't understand the payload content.
Power and Sensor Data Anomalies
For devices that are connected to a battery or external power, the IoT Bridge can detect if a device is powered off, was the battery disconnected. When the power is reconnected, it can detect if the source power level different from before the disconnection? This may indicate that the device was swapped to an alternate machine. Simply alerting that a device has been taken offline may be enough to trigger a security investigation depending on the device's role.
Firmware and Configuration Compliance
One of the most significant security risks in LPWA IoT is fleet drift. Devices operating with outdated firmware, misconfigured settings, or security parameters that don't align with fleet-wide policy. The IoT Bridge continuously processes device registrations and data reports, building a real-time picture of fleet health.
This enables detection of:
- Outdated firmware: Devices running versions with known vulnerabilities that haven't received OTA updates
- Configuration drift: Devices whose reporting intervals, sensor thresholds, or communication parameters differ from the fleet baseline
- DTLS mismatches: Devices with incorrect or expired pre-shared keys, unsupported cipher suites, or security profiles that don't match policy
- Rogue devices: Endpoints attempting to register with credentials that don't match known fleet inventory
Intelligent Filtering and Alerting
The IoT Bridge's trigger-based architecture enables custom security logic that operates on decoded device data. Triggers are scripts that evaluate incoming events against security policies and execute actions in response — from enriching data with security metadata, to logging events for audit, to actively blocking device access.
This goes far beyond what a firewall rule can express. A firewall rule might say "allow UDP traffic from this IP range to this destination on this port." An IoT Bridge trigger can say "if this device reports a firmware version older than 2.4.1, and its DTLS cipher suite has been downgraded from the fleet standard, log a critical security event, notify the SOC, and suspend the device's application access."
SIEM Integration: Bridging IoT Security into Enterprise IT Operations
Perhaps the most strategically important capability of the IoT Bridge's security layer is its integration with enterprise Security Information and Event Management (SIEM) systems.
IT security teams manage their threat landscape through SIEMs — platforms like Splunk, Microsoft Sentinel, IBM QRadar, and others that aggregate, correlate, and act on security events across the enterprise. These teams have established playbooks, escalation procedures, and response workflows.
LPWA IoT has traditionally been invisible to these systems. The devices don't generate syslog. They don't produce Windows event logs. They don't speak the language of enterprise security operations.
The Tartabit IoT Bridge changes this. By decoding device data, applying security policies, and generating structured security events, the IoT Bridge feeds LPWA IoT security telemetry directly into the SIEM. This means:
- IoT security events appear alongside IT security events in a single pane of glass
- Existing correlation rules can incorporate IoT device behavior
- SOC analysts can investigate IoT security incidents using familiar tools
- Automated response playbooks can include IoT-specific actions like SIM suspension or device quarantine
The result is that LPWA IoT security becomes a managed, operational concern — not a separate silo that IT teams don't have visibility into.
Putting It All Together: Defense in Depth for LPWA IoT
No single security layer is sufficient. Each layer in this architecture provides capabilities that the others cannot:
| Capability | Layer 1: Network (Aeris) | Layer 2: Firewall (Palo Alto / Fortinet) | Layer 3: Application (Tartabit IoT Bridge) |
|---|---|---|---|
| Traffic-level threat detection | ✅ | ✅ | - |
| IP/destination blocking | ✅ | ✅ | - |
| Device discovery & classification | - | ✅ | ✅ |
| Zero Trust network access | ✅ | ✅ | - |
| OT protocol DPI (Modbus, BACnet) | - | ✅ | - |
| LPWA protocol DPI (CoAP, LWM2M, DTLS) | - | - | ✅ |
| Payload decoding (CBOR, binary) | - | - | ✅ |
| Firmware version auditing | - | - | ✅ |
| Configuration drift detection | - | - | ✅ |
| Location data validation | - | - | ✅ |
| DTLS parameter inspection | - | - | ✅ |
| SIEM event generation (decoded IoT) | - | - | ✅ |
| SIM-level suspension | ✅ | - | ✅ (via integration) |
| Application-level device blocking | - | - | ✅ |
The three layers are complementary, not redundant. Network-layer security catches threats at the pipe level before they reach your infrastructure. Enterprise firewalls enforce perimeter policy and provide broad device visibility. The IoT Bridge provides the deep, protocol-aware intelligence that only comes from understanding what the device is actually saying.
A Practical Example: Fleet Asset Tracking
Consider a fleet of 10,000 NB-IoT asset trackers deployed across a logistics network. Each device communicates via CoAP over DTLS, reporting GNSS location, battery status, and sensor data every 15 minutes through LWM2M objects.
Layer 1 (Aeris Watchtower) monitors the cellular traffic and detects that 12 devices have begun communicating with an IP address associated with a known botnet command-and-control server. Watchtower blocks these destinations and alerts the enterprise.
Layer 2 (Enterprise Firewall) classifies the tracker traffic and enforces a policy that only allows UDP communication to the approved IoT Bridge endpoint on the expected port. Any device attempting to communicate with unauthorized destinations inside the enterprise network is blocked.
Layer 3 (Tartabit IoT Bridge) decodes the LWM2M registration from every device and identifies that 340 devices are still running firmware version 1.8.3, which contains a known vulnerability in its DTLS implementation. It also detects that 7 devices are reporting GNSS coordinates that place them in the middle of the ocean — suggesting either device malfunction or data spoofing. The IoT Bridge generates security events for both conditions, sends them to the enterprise SIEM, and triggers an automated workflow to schedule OTA firmware updates for the affected devices while flagging the location anomalies for SOC investigation.
No single layer could have caught all three issues. Together, they provide comprehensive coverage.
Getting Started with Layered LPWA IoT Security
Building a three-layer security architecture doesn't require ripping out existing infrastructure. Each layer can be adopted incrementally:
-
Evaluate your cellular provider's security offerings. If you're already on Aeris, Watchtower can be enabled with zero device-side changes. Other carriers are developing similar capabilities — ask about network-level threat detection and Zero Trust enforcement.
-
Ensure your enterprise firewall has IoT-aware policies. If you're running Palo Alto or Fortinet NGFWs, enable their Device Security or OT Security subscriptions. Configure policies that restrict IoT device traffic to approved destinations and protocols.
-
Deploy the Tartabit IoT Bridge as your application-layer security platform. The IoT Bridge integrates into your existing architecture — whether deployed as SaaS on Azure or AWS, or as a private instance within your infrastructure. Configure triggers to validate device data, audit firmware compliance, and generate security events for your SIEM.
The IoT Bridge supports flexible deployment options including public SaaS, private deployments for customers using private APNs and VPNs, and hybrid configurations that meet strict regulatory requirements in healthcare, utilities, and government.
Conclusion
The era of treating LPWA IoT security as an afterthought is over. With IoT malware attacks surging, regulatory frameworks tightening, and the consequences of breaches extending into physical safety, enterprises need a security architecture that matches the complexity of their IoT deployments.
Network-layer security from cellular providers like Aeris catches threats at the pipe. Enterprise firewalls from Palo Alto and Fortinet enforce perimeter policy and device classification. But neither can see inside the constrained, specialized protocols that LPWA IoT devices actually use.
The Tartabit IoT Bridge closes that gap. As an application-layer security platform with native understanding of CoAP, DTLS, LWM2M, LoRaWAN, and proprietary device codecs, it delivers the deep packet inspection that LPWA IoT demands — and feeds that intelligence directly into the enterprise SIEM systems that IT teams already rely on.
Three layers. One architecture. Complete coverage.